Education
Resource Library
A security program is only as strong as its weakest link. SBS strongly believes in the power of education and security awareness training when it comes to a strong information security program.
Build Your Cybersecurity Culture
Get Free Resources
Share these cybersecurity training tools with your employees and customers to nurture a strong cybersecurity culture at your organization.
-
All
-
eBook
-
Poster
-
Tip Sheet
-
Infographic
-
Other

eBook
AI Roadmap
eBookAI RoadmapRead More

eBook
AI Governance Readiness Checklist
eBookAI Governance Readiness ChecklistRead More

eBook
Fraudacity Files
eBookFraudacity FilesRead More

eBook
The State of Cybersecurity in Credit Unions
eBookThe State of Cybersecurity in Credit UnionsRead More

Poster
The Golden Rule of Email
PosterThe Golden Rule of EmailDownload
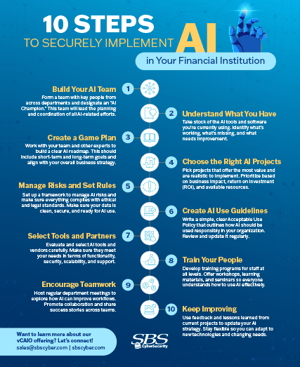
Tip Sheet
10 Steps to Securely Implement AI in Your Financial Institution
Tip Sheet10 Steps to Securely Implement AI in Your Financial InstitutionRead More
eBook
Essential Cybersecurity Best Practices
eBookEssential Cybersecurity Best PracticesDownload

eBook
5 Common Cybersecurity Mistakes Financial Institutions Overlook
eBook5 Common Cybersecurity Mistakes Financial Institutions OverlookRead More
eBook
CEO's Cybersecurity Glossary
eBookCEO's Cybersecurity GlossaryRead More
eBook
Security Awareness Toolkit
eBookSecurity Awareness ToolkitDownload
eBook
8 Emergency Preparedness Testing Scenarios
eBook8 Emergency Preparedness Testing ScenariosDownload
eBook
Incident Response Preparedness: 50+ Checklist Items
eBookIncident Response Preparedness: 50+ Checklist ItemsDownload
eBook
You Are a Technology Company
eBookYou Are a Technology CompanyDownload
eBook
FDIC InTREx: What Documentation Are You Expected to Have?
eBookFDIC InTREx: What Documentation Are You Expected to Have?Download
eBook
Cybersecurity Tips
eBookCybersecurity TipsDownload
eBook
Defense in Depth Checklist Controls
eBookDefense in Depth Checklist ControlsDownload

eBook
34 Unique Ideas to Create a Culture of Cybersecurity
eBook34 Unique Ideas to Create a Culture of CybersecurityDownload
eBook
5 Key Questions to Consider When Researching a vCISO
eBook5 Key Questions to Consider When Researching a vCISODownload

Infographic
The 3 Ws of Spotting Phishing Scams
InfographicThe 3 Ws of Spotting Phishing ScamsDownload

Infographic
Don't Take the Bait
InfographicDon't Take the BaitDownload
Tip Sheet
Microsoft 365 Security Suggestions
Tip SheetMicrosoft 365 Security SuggestionsDownload
Tip Sheet
Investigating Phishing Emails
Tip SheetInvestigating Phishing EmailsDownload

Tip Sheet
Stronger Passwords, Stronger Security
Tip SheetStronger Passwords, Stronger SecurityDownload
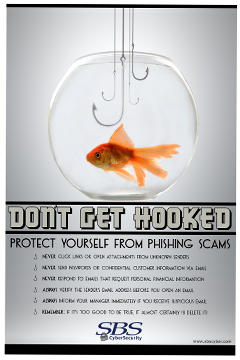
Poster
Don't Get Hooked
PosterDon't Get HookedDownload

Infographic
Information Technology vs. Information Security
InfographicInformation Technology vs. Information SecurityDownload

Infographic
10 Key Ideas to Build a Cybersecurity Culture
Infographic10 Key Ideas to Build a Cybersecurity CultureDownload

Infographic
The SBS Risk Management Method
InfographicThe SBS Risk Management MethodDownload
Other
Sounds of Security
OtherSounds of SecurityListen

Other
Cybersecurity Heroes Coloring Pages
OtherCybersecurity Heroes Coloring PagesRead More
Webinars
June 03, 2026
Hacker Hour: The Future of SIEM in 2026
Uncover how modern SIEM strategies address AI-generated data, compliance requirements, and storage challenges.
Watch Webinar
April 30, 2026
Hacker Hour: Winning Over the Locker Room and the Boardroom
Discover what an NFL team captain can teach cybersecurity leaders about trust, influence, and leadership.
Watch Webinar
March 26, 2026
Hacker Hour: Internal Penetration Testing — Inside an Attacker’s Playbook
Using real-world penetration testing scenarios, we'll discuss how attackers pivot through networks, abuse credentials, and bypass common security controls.
Watch Webinar
May 11, 2026
Cyber Showcase: From Spreadsheets to Strategy — Connecting Your ISP with TRAC
Move beyond spreadsheets to manage your information security program with a fully integrated, streamlined approach using TRAC.
Watch Webinar
March 26, 2026
Cyber Showcase: Spring Cleaning M365 — What to Fix, What to Keep, What to Watch + Converge Preview
Spring is the perfect time to clean up M365 security clutter. Discover common misconfigurations and how SBS’s M365 Hardening Assessment helps reduce risk.
Watch Webinar
February 12, 2026
Cyber Showcase: Revisiting CRI — A Guide for Procrastinators
Revisit the CRI Profile—its purpose, alignment with other risk frameworks, and whether it truly fits as your long-term replacement.
Watch Webinar

Get Certified
Looking to enhance your cyber education with a focus on the banking industry? Look no further than the SBS Institute! Choose a course tailored to your specific role for a flexible and targeted learning experience.
Blog Posts
Lindsey HullJune 03, 2026
Governing AI Agents: When Your Assistant Recommends a Phishing Email
AI agents now read, write, and act on your documents and email. Learn the risks emerging across regulated organizations and the controls that keep AI use safe.
Start Reading
SBS CyberSecurityJune 03, 2026
Hacker Hour: The Future of SIEM in 2026
Uncover how modern SIEM strategies address AI-generated data, compliance requirements, and storage challenges.
Start Reading
SBS CyberSecurityJune 01, 2026
Banking Leaders Turn to SBS CyberSecurity CEO Chad Knutson to Cut Through the AI Hype
SBS CyberSecurity CEO Chad Knutson helps banking leaders cut through AI hype, presenting at the AI in Banking Summit and GSB's AI Innovation Series this June.
Start Reading
What would you like to do next?
Hear From Our Clients
See what companies like yours are saying about partnering with SBS!
Read Testimonials
View All Blogs
Get resources that simplify complex concepts, offer practical tips, and keep you informed.
Go to the Blog
![Icons_HackerHour]() Free Hacker Hour Webinar Series
Join us for this interactive and engaging cybersecurity training experience.
See Hacker Hours
Get Certified
Join the growing community of professionals committed to strong cybersecurity and career advancement with an SBS Institute certification.
Get the Details
Start My Journey
Book a meeting with one of our experts to learn more about partnering with SBS.
Book a Meeting
Free Hacker Hour Webinar Series
Join us for this interactive and engaging cybersecurity training experience.
See Hacker Hours
Get Certified
Join the growing community of professionals committed to strong cybersecurity and career advancement with an SBS Institute certification.
Get the Details
Start My Journey
Book a meeting with one of our experts to learn more about partnering with SBS.
Book a Meeting
![Icons_TRAC]() Simplify Compliance
Learn how TRAC takes the guesswork out of cybersecurity risk management and compliance.
Get the Details
Simplify Compliance
Learn how TRAC takes the guesswork out of cybersecurity risk management and compliance.
Get the Details

